Quick summary
- SERoundtable.com has been hit with a product spam injection attack on the root domain.
- Thousands of
?product_id=URLs were injected showing sneakers, car parts, hardware, and home products with full product schema. - The spam URLs are returning 404 now but remain indexed in Google.
- The site runs on PHP, not WordPress — so the compromise likely came through a vulnerable PHP dependency, server-level access, or a neighboring site on the same hosting.
- Prefix removal via GSC is uncertain because the URLs use query parameters (
?product_id=), and it’s unclear how Google handles prefix matching with?at scale. - Before acting on removals, the safest move would be to ask Google Search Central Community for guidance on whether prefix removal covers query parameter patterns.
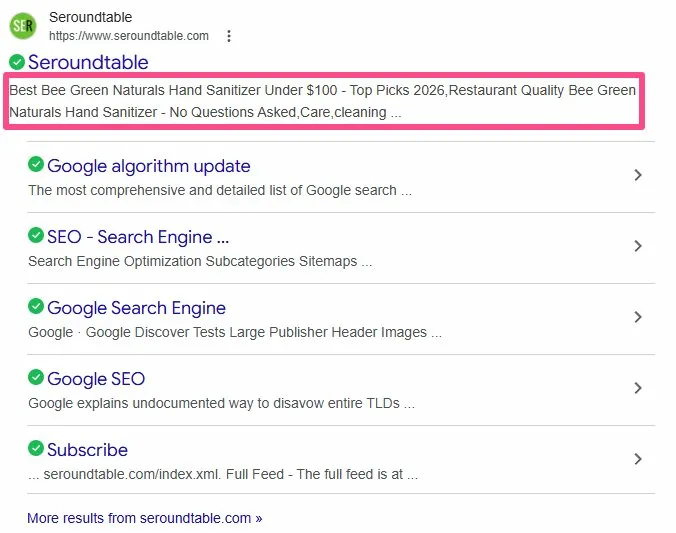
Search Engine Roundtable — Barry Schwartz’s SEO news site that’s been running since 2003 and has over 4.24 million linking domains — appears to have been compromised with a product spam injection attack. The hack is sitting right on the root domain, and Google has indexed thousands of the spam URLs.
The site itself is still publishing normally. Barry posted his daily search forum recap as recently as March 9, 2026. The editorial side is untouched. But run a few site searches in Google and the picture changes fast.
It’s been two days and still Thousands of Fake URLs Still Indexed!
What shows up when you search
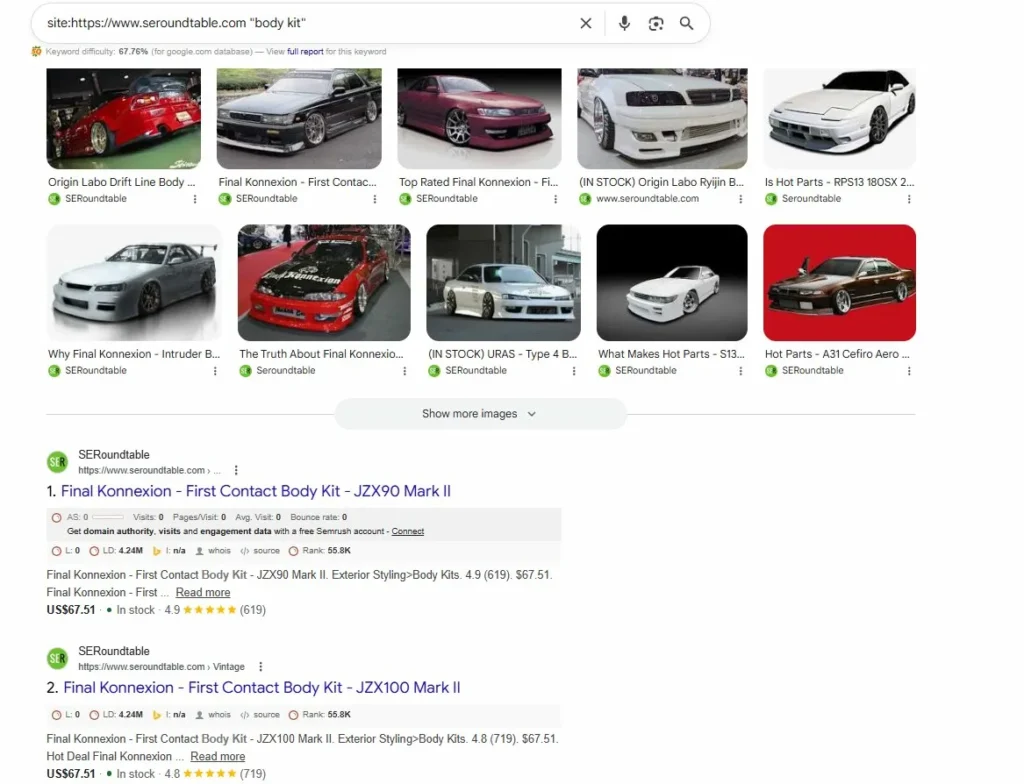
Search site:https://www.seroundtable.com/?product_id= in Google, Bing Search or Google Images and you get results like these:
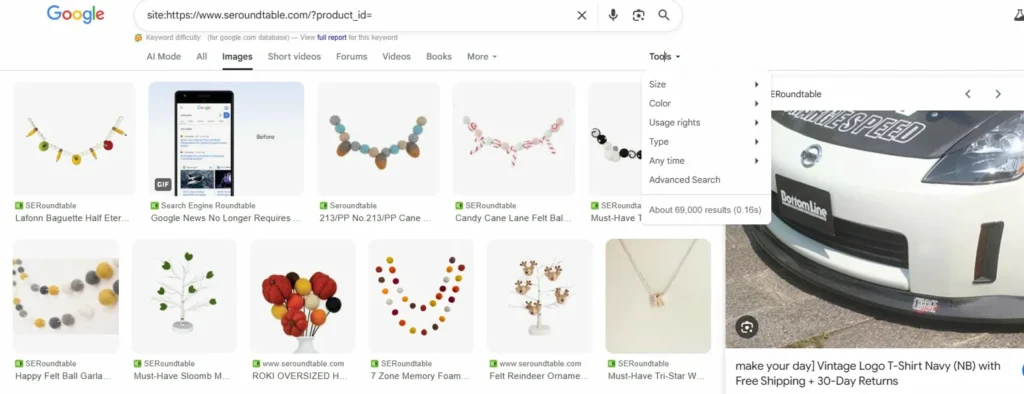
Felt ball garlands. Candy cane ornaments. Memory foam products. All showing under the seroundtable.com domain.
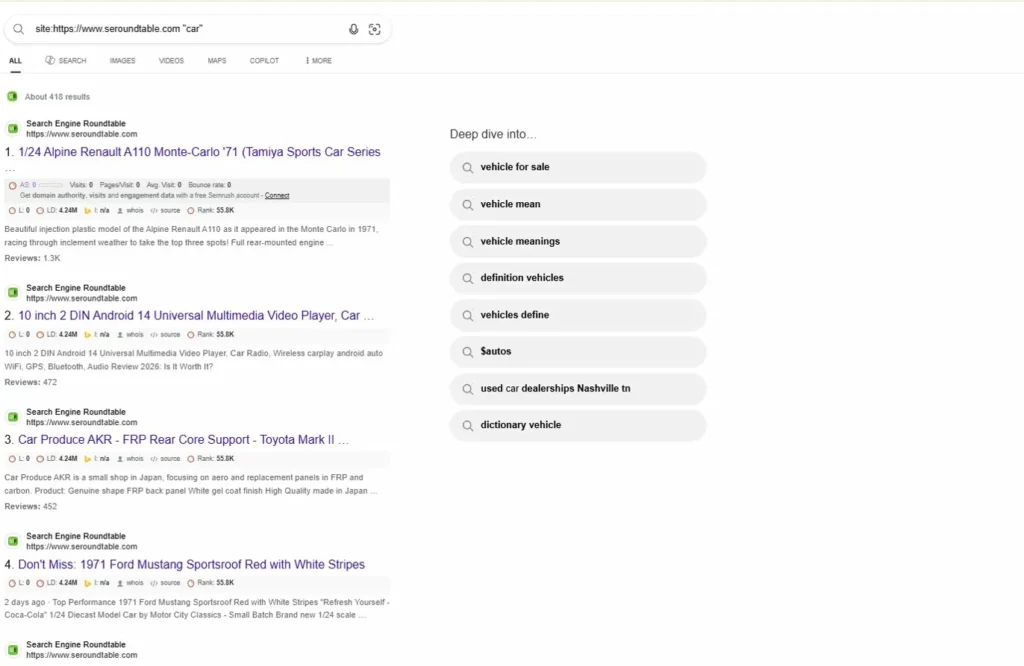
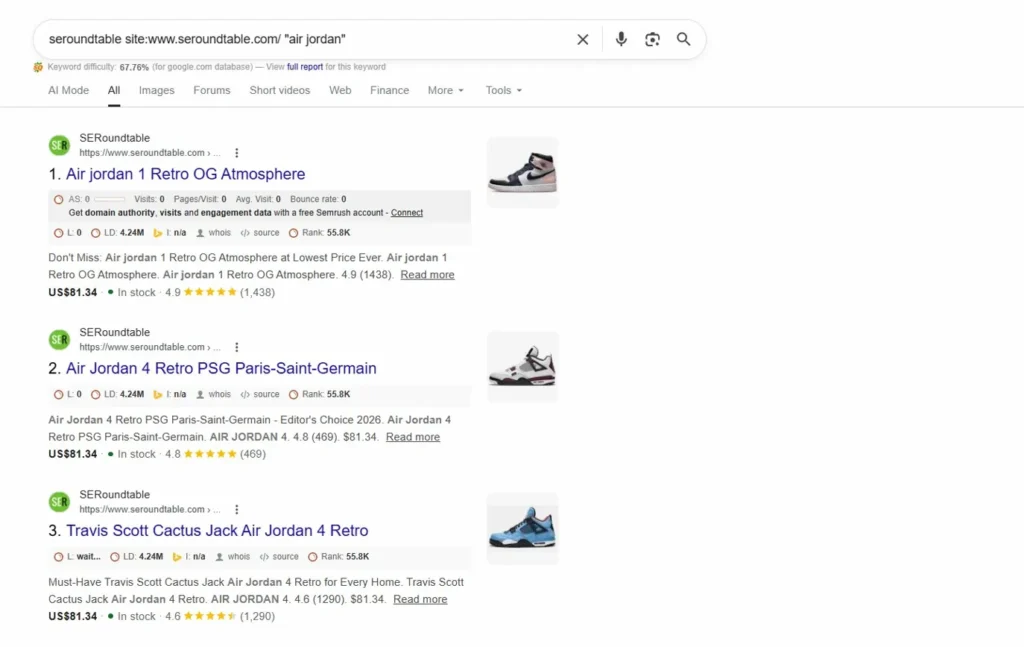
Switch to regular search with site:www.seroundtable.com/ "air jordan" and it gets worse.
Full product listings. Air Jordan 1 Retro OG Atmosphere at $81.34 with 4.9-star ratings and 1,438 reviews. Air Jordan 4 Retro PSG Paris-Saint-Germain. Travis Scott Cactus Jack. All of it ranking under seroundtable.com with product schema markup — prices, availability, review stars.
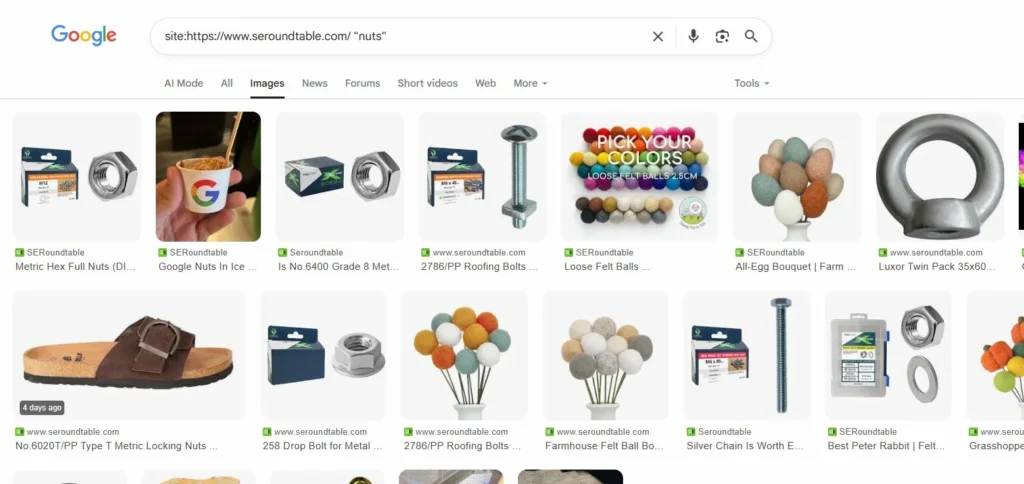
Try "nuts" and you’ll find metric hex nuts, roofing bolts, and drop bolts.
Search "In stock" on the domain and you get car body kits — URAS Type 4 Body Kits for S14, Origin Labo Ryijin Body Kits, front fenders for Toyota.
None of this content belongs on an SEO news site. Somebody injected product pages at scale.
Just to be clear it’s not Google issue or any glitch but a proper target hacking. As bing also crawled these hacked pages.
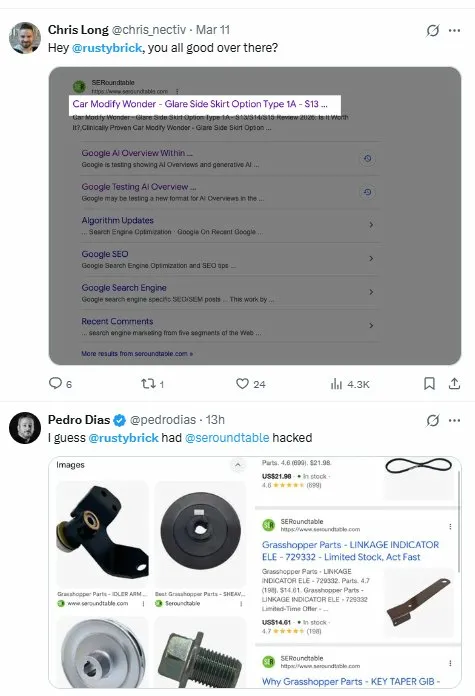
I also see chatter on X for this.
How the URLs are structured
Every spam page follows the same pattern:
https://www.seroundtable.com/?product_id=10126012659027The product_id parameter is appended to the root domain. There are thousands of these. Each one carried a different product — sneakers, hardware, car parts, home décor — with full product markup including pricing and fake reviews.
The URLs are returning 404 now, which means some level of cleanup has happened or the injected code has been removed. But Google hasn’t caught up. These pages are still sitting in the index, still appearing in search results, still carrying the seroundtable.com brand alongside products that have nothing to do with search engine news.
How were they compromised
SERoundtable doesn’t run WordPress. Check the tech stack and you’ll see PHP-based custom build with Cloudflare, Google Analytics, Snowplow Analytics, and standard publishing tools.
[Insert Image 7 — SERoundtable homepage with tech stack overlay showing PHP, Cloudflare, analytics tools]
No WordPress means this wasn’t a vulnerable plugin or a theme exploit — which is the usual suspect in most site hacks. With a PHP-based setup, the possible entry points narrow down to a few scenarios:
- A compromised PHP library or dependency that the site relies on.
- A server-level breach — if another site on the same shared hosting environment was compromised (especially one running WordPress), the attacker could have moved laterally to seroundtable.com.
- A direct vulnerability in a PHP script or an exposed admin endpoint.
Without access to their server logs, there’s no way to confirm the exact vector. But the injection landing on the root level — not inside a subdirectory or a subfolder — suggests the attacker had meaningful access, not just a surface-level exploit.
The tricky part about cleaning this up
Here’s where it gets interesting from a technical SEO standpoint.
Normally when a site gets hit with spam page injection, you clean the files, make the URLs return 404, and then use Google Search Console’s URL Removal tool to accelerate deindexing. For path-based spam like /shop/product/fake-item you can submit a prefix removal for /shop/ and Google clears the entire directory.
But these URLs use query parameters. The structure is ?product_id=XXXXX appended to the root. That raises a real question: if you submit a removal request for https://www.seroundtable.com/?product_id= — does Google treat the ? as part of a prefix match? Or does it break the pattern matching?
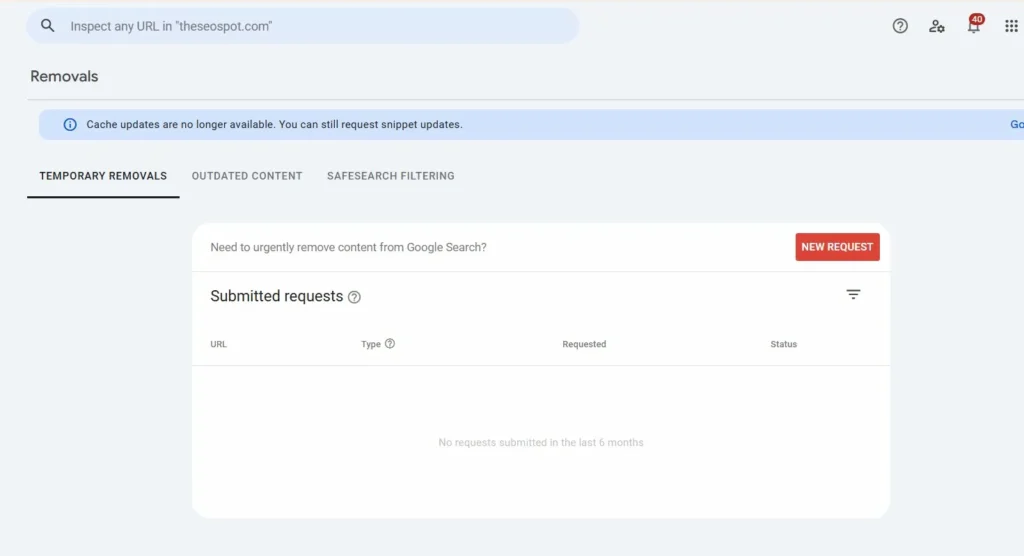
I’m genuinely not sure how Google handles prefix removal when query parameters are involved at this scale. Thousands of unique ?product_id= URLs is not something you can remove one by one. And bulk removal has limits.
Honestly, before doing anything with removals in this specific case, I’d post the question in the Google Search Central Help Community and wait for a response from one of the product experts. The ? parameter prefix matching behavior isn’t something that’s well-documented for this kind of mass spam cleanup, and getting it wrong could either do nothing or — worse — accidentally request removal of the root domain itself.
No visible parasite SEO impact — but thousands of indexed spam URLs remain
From what’s visible externally, there’s no noticeable impact from this hack in terms of parasite SEO actually ranking for commercial terms and driving traffic through seroundtable.com. The spam pages exist in the index but don’t appear to be performing as the attacker likely intended.
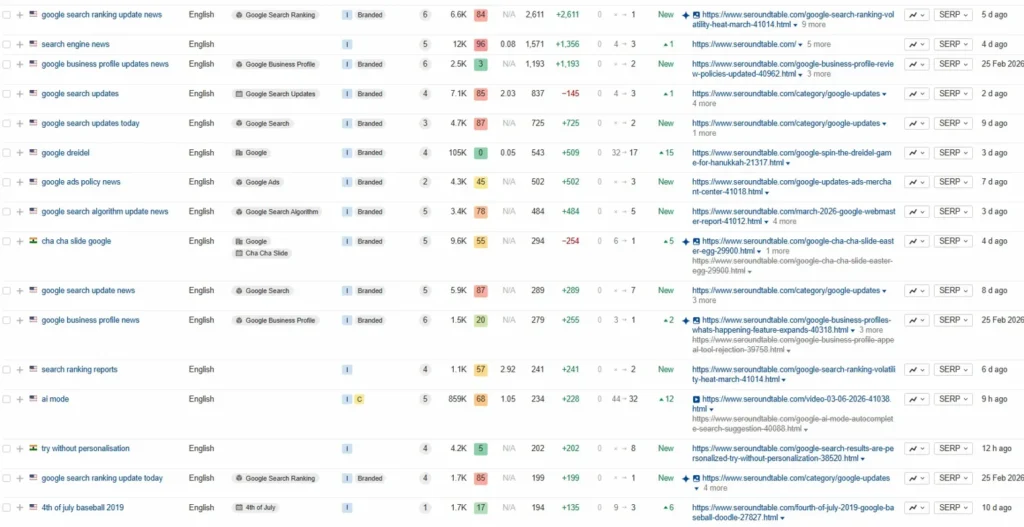
That said, thousands of indexed URLs showing fake products with pricing and review schema under your domain is not a situation anyone wants to sit with for long. Even if it’s not affecting core rankings right now, the indexed spam pages still carry the site’s branding, and anyone doing a site search will see them immediately.
The 404 status on those URLs should eventually lead to Google dropping them from the index. But “eventually” with Google can mean weeks or months, and the volume here is massive.
References
- Google Search:
site:https://www.seroundtable.com/?product_id=— accessed March 13, 2026 - Google Search:
site:www.seroundtable.com/ "air jordan"— accessed March 13, 2026 - SERoundtable.com tech stack — observed via Wappalyzer, March 2026
- Google Search Console URL Removal documentation — https://support.google.com/webmasters/answer/9689846