What is The Future of Proxies?
Proxy servers currently play crucial roles in a myriad of use cases, including security, web scraping, web server performance, and more. As the demands of technology change and grow, however, proxy servers will be required to evolve at an equal pace. As a result, proxies will likely be more secure,
 Ahsan SoomroHead of SEO4 min read
Ahsan SoomroHead of SEO4 min read
Proxy servers currently play crucial roles in a myriad of use cases, including security, web scraping, web server performance, and more. As the demands of technology change and grow, however, proxy servers will be required to evolve at an equal pace. As a result, proxies will likely be more secure, reliable, and better suited to match the increased performance of future systems.
What is a Proxy
A proxy or proxy server is a computer hardware, or software found midway between a computer and a web server. It routes all internet traffic through itself, acting like the first figurative port of call for all outgoing requests and incoming server responses. In addition to being the first recipient, the proxy server hides the requests’ real IP address and assigns another new IP address which anonymizes the browsing.
There are different types of proxy products, which differ based on the type of IP address assigned and the criteria used to complete the assignment. The various proxy types are:
- Datacenter proxies
- Residential proxies
- Forward proxies
- Reverse proxies
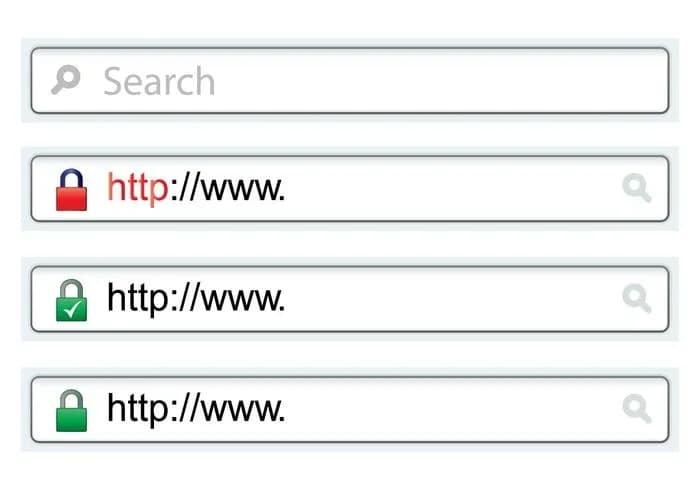
- HTTPS/HTTP proxies
- SOCKS/SOCKS5 proxies
- Transparent proxies
- Rotating proxies
- Static proxies
- Shared proxies
- Dedicated proxies
- Anonymous and high-anonymity proxies
And as discussed below, these proxy products offer numerous advantages.
Advantages of Proxy Servers
Proxy products offer the following benefits:
- Security: Proxy servers act as the first port of call, ensuring that a local network is not connected directly to the internet. This way, proxies enhance security by preventing direct attacks on a local network.
- Anonymity: Proxy products anonymize web browsing by hiding the real IP address and assigning a new unique identifier. This prevents IP blocking, making them handy in web scraping and ad verification.
- Server performance: Proxies enhance server performance by balancing the load among multiple proxy servers. This ensures visitors are connected to the nearest proxy, increasing the loading speed. It also protects the web server by preventing Distributed Denial-of-Service (DDoS) attacks.
- Access to geo-blocked content
- Content filtering and control: Proxy products such as transparent proxies can be used to block access to certain websites. This boosts productivity in the workplace. In addition, it protects the local network as it can be used to block websites that may contain malware. At the same time, proxies, such as HTTP proxies, filter incoming responses and emails to ensure they do not contain phishing links.
- Caching: Reverse proxies and server-side HTTP proxies store frequently accessed files, boosting the loading speed and freeing up the bandwidth for other less common requests.
- Fast data sharing: SOCKS and SOCKS5 proxies have great loading speeds, which make them ideal for peer-to-peer file sharing and streaming. Click here to see more proxy product features and information.
Future of Proxies
The evolution of technology is bound to place even more demands on proxy providers to provide reliable, safe, and fast proxy servers. In addition, proxies will have to evolve to suit the business needs of the ever-changing digital environment. For instance, as more businesses embrace artificial intelligence (AI) and machine learning (ML), proxies will have to incorporate aspects of AI and ML to boost performance, reliability, and security. For instance, anti-scraping and bot detection techniques are bound to evolve. This means proxies will also have to evolve to prevent IP blocking.
Fundamentally, however, the future of proxies lies in security. This comes against a backdrop of worrying statistics. Firstly, the volume of IoT (Internet of Things) cyberattacks is expected to double between 2022 and 2025. Furthermore, cyberattacks on businesses are becoming more complex, targeted, and regular.
A study assessing the vulnerability of small to medium-sized companies showed that 45% had ineffective processes to mitigate against attacks. Additionally, 66% noted they had experienced a cyberattack in the last year, while 69% observed the attacks are becoming more targeted. Additionally, they listed phishing as the most common type of attack (57%), followed by compromised/stolen devices (33%) and credential theft (30%).
Source: https://www.keeper.io/hubfs/PDF/Cybersecurity%20in%20the%20Remote%20Work%20Era%20-%20A%20Global%20Risk%20Report.pdf
These statistics underscore the need for companies to implement cybersecurity measures. While proxies already play an important role in enhancing security presently, this role is expected to expand even more.
Present and Future Uses of Proxies
Proxies offer security (both currently and in the future) in the following ways.
- Preventing phishing attacks by filtering content such as server responses and emails; in fact, proxies can interpret data packets, providing visibility into each connection between a client and a web server. This role is expected to become even more advanced as a result of the introduction and adoption of programmable proxies.
- Balancing the incoming requests among various servers (load balancing) to prevent DDoS attacks
- Blocking access to specific websites that may be unsecured or have malicious content
- Preventing fraud by facilitating web scraping (brand monitoring) and ad verification
Conclusion
As technology evolves to better address the emerging needs of the digital economy, proxy servers will also experience an evolution. As a result, proxy products will need to be more resilient, secure, and post exemplary performance. This will make them particularly useful, especially in light of projections that show that cyberattacks will increase significantly in the future.
You may also like
Send me your site
I'll tell you honestly what's broken. If we can't help, I'll tell you who can.
Free · 45 min · no obligation